Azure Active Directory (AAD) is a cloud-based identity and access management service. It enables your employees to access external resources, such as Microsoft 365, the Azure portal, and thousands of other SaaS applications. With an increasing number of businesses migrating to Azure Active Directory to take advantage of the benefits that cloud platforms provide, we want you to be sure your environment is secure. In this article we cover some Azure Active Directory security best practices to keep you covered.
Azure Active Directory security best practices
Plan for routine security improvements
As cyber security threats continue to grow, we need to constantly up our game when it comes to security. It is important to build your cloud and identity management framework in a way that regularly shows growth and allows you to secure your environment in new ways.
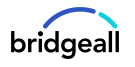
This is where you can use identity secure score. The identity secure score is a set of recommended security controls that Microsoft publishes that work to provide you with a numerical score to objectively measure your security posture and help plan future security improvements. You can also view your score in comparison to those in other industries as well as your own trends over time. You can see more about identity secure score here.
People management
As part of people management, it is imperative that organisations maintain their user base within AAD. What we mean here is the process of movers/joiners/leavers. When a user leaves the company, as a minimum their account should have its password reset, privileges removed and sign-in disabled. Remember, an active/unmonitored account for a user that has left the company represents a security vulnerability and a potential target for hackers.
Multi-factor authentication
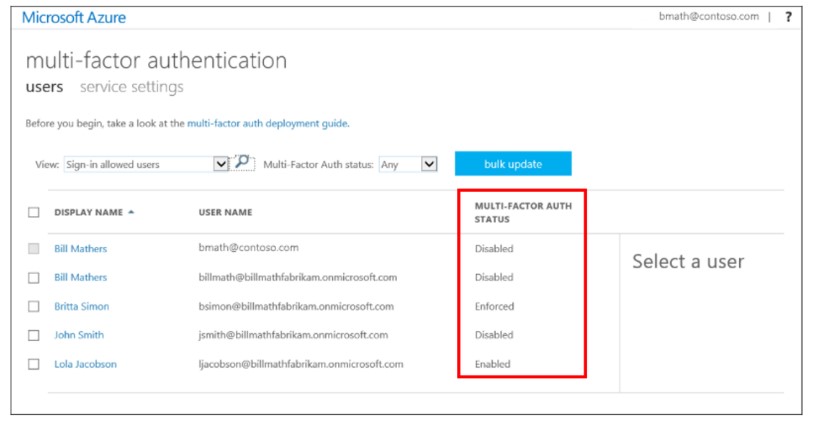
Multi-factor authentication (MFA) requires secondary confirmation from the user and enabling this for your user accounts can significantly reduce the risk of compromised accounts leading to critical data loss. This can be presented to your users in a number of ways whether it be SMS, phone call or an authenticator application which can be locked by biometrics. You can learn more about per-user MFA here.
Conditional access
To balance security and productivity, you need to think about how a resource is accessed before you can make a decision about access control. With Azure AD Conditional Access, you can address this. By using conditional access, you can create specific conditions and rules that must be met for a user to successfully authenticate with your AAD and access your company data. Some examples here would be:
- Locking access to your data down to your company public IP addresses only
- You could mandate only company managed devices can access data
- Prevent access from devices that do not have an up-to-date operating system installed
These are just a few examples, however it’s possible to be very granular with conditional access to ensure data can only be accessed under your desired rules.
User access
Lastly, we have user access. Azure AD by nature enables you to collaborate with users from inside your organisation and with external users. Users can join groups, invite guests, connect to cloud apps, and work remotely from their work or personal devices. This can lead to access permissions for users/groups being out of date, no longer relevant and potentially insecure. As an advanced feature of Azure AD, it’s possible to schedule and conduct regular access reviews to maintain correct group membership and permissions helping reduce security risk.
If you’re looking to secure your Azure Active Directory environment and don’t know where to start, we can help. We offer a full range of cloud consultancy, migration and support services to help your organisation move to the cloud. See a full range of our Azure services here or complete the contact form here and our team will be in touch.